- How To Crack Trial Software With Ollydbg Tutorial Beginners Pdf
- How To Crack Trial Software With Ollydbg Tutorial Beginners Photo Editing Software
- How To Crack Trial Software With Ollydbg Tutorial Beginners For Beginners
- How To Crack Trial Software With Ollydbg Tutorial Beginners Tutorial
Using API Monitor to crack copy protected software
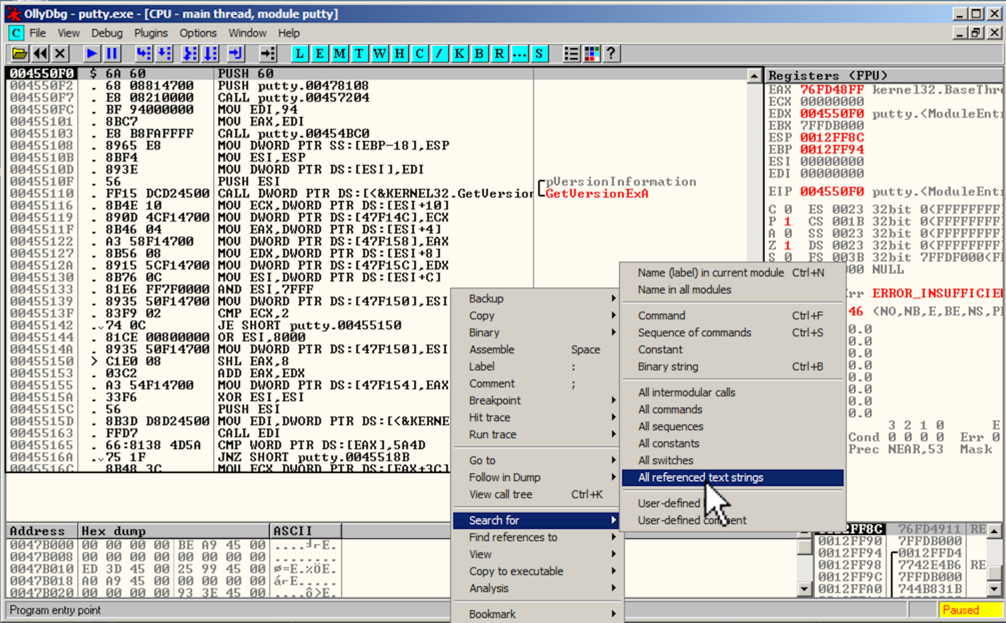
OllyDbg is a 32-bit assembler level analyzing debugger for Microsoft Windows applications. Emphasis on binary code analysis makes it particularly useful in cases where the source is unavailable. Generally, it is used to crack the commercial softwares. To open it, go to Applications → Reverse Engineering → ollydbg. Reversing with Olly. With our tour of Olly behind us, we are now ready to start doing some real work: reversing and cracking a “trial” piece of software. In this tutorial, we will look at one of the most widely used and free debuggers, OllyDbg. OllyDbg is a general purpose Win32 user-land debugger. Software cracking groups have been around for a long time. Many people will think that they are unethical because they are defeating the software licensing system to illegally reset a trial software (shareware) or turn it into an fully functional program without having to purchase the license. An introduction to Reverse Engineering, a behind the scenes of malware analysis, and using tools like Ollydbg. As a practical example we'll be looking into t. Beginners usually have a hard time picking one among ollydbg, x64dbg or IDA. This is a perfect guide for those who are confused which to choose. Before diving deep into which one to choose & when to choose, let’s first understand some basic things on which compare is done.
This tutorial demonstrates how to use API Monitor to crack copy protected software.
Software cracking is the modification of software to remove or disable features which are considered undesirable by the person cracking the software, usually related to protection methods: copy protection, trial/demo version, serial number, hardware key, date checks, CD check or software annoyances like nag screens and adware – Wikipedia
For this tutorial we will be using Mirial Softphone which is a HD video conferencing application. This tutorial is for educational purposes only, so please do not use this to create or distribute a cracked copy of the software.
How To Crack Trial Software With Ollydbg Tutorial Beginners Pdf

When you first install the application, it prompts you for a license file. After installing the license you have 30 days to evaluate the application. The expiration date is displayed on this screen; in our case it is March 15, 2011.
Oct 27, 2011 TypingMaster Pro is a professional typing tutor that helps you double your typing speed. In a few hours you will master the efficient touch typing skill. As a result you will save hours and hours of time! Fast downloads of the latest free software! TypingMaster Pro is a professional typing tutor that helps you double your typing speed. In a few hours you will master the efficient touch typing skill. Old versions of TypingMaster Typing Tutor Pro. Latest Version. TypingMaster Typing Tutor Pro 7.10 released: 05 Jun 2013 - 7 years ago old Versions. TypingMaster Typing Tutor Pro 7.01. Typing master 2002 old version download. Mar 26, 2014 TypingMaster Pro for Windows is your personal typing tutor featuring 5 typing courses, tests, personalized reviews, games and much more. Last update 26 Mar. 2014 old versions Licence Free to try OS Support Windows XP, Windows Vista, Windows 7. Download typing master full version pc for free. Education software downloads - TypingMaster by TypingMaster Inc and many more programs are available for instant and free download.
Trial applications usually store license information in either the registry or on the file system. Since this application prompted us for a license file, we know that it uses the file system. Start up the 32-bit version of API Monitor and enable API’s from the File Management category.
Select Hook Process from the File menu to start monitoring the application.
API Monitor will start monitoring and displaying API calls. The application should now display a message indicating that it is an evaluation version. Hit cancel to quit the application.
Now that we have captured the API calls made by the application, we need to find the one that reads the license file. Scan through the calls in the API summary view until you find the right one.
The application is reading from mirial.lic file. The name suggests that it might be a license file, so let’s open it up.
We’ve located the license file and it has the expiration date in it.
Modify the expiration date in the license file to 2012-03-15 and save the file. Now launch the application again. The application should now display an error indicating that the license is invalid. Hit cancel to quit the application.
Our next step is to start debugging the application right after it has read the license file. From Step 3, we know that the application uses CreateFileA to open the file and ReadFile to read the file. Setup a Breakpoint on CreateFileA and launch the application in API Monitor. The breakpoint will be hit multiple times; continue until you reach the one that opens the license file.
Switch back to API Monitor and enable a post-call breakpoint on the ReadFile API and disable the CreateFileA breakpoint. Now hit Continue to let the application run. API Monitor should now display the ReadFile breakpoint.
Now hit the Break button to have API Monitor generate a breakpoint in the application. You should now be able to attach to the application using a debugger.
Your debugger should now display disassembled instructions from the application

If you look at the call stack, you’ll notice that the current frame is in apimonitor-drv-x86.sys. Use the debugger to step out until you reach code in the application. Il 2 sturmovik battle of normandy.
The debugger is currently at a location right after the application has finished reading the license file and before it checks the validity of the license. We need to locate the code that performs this check and disable it.
The most common software crack is the modification of an application’s binary to cause or prevent a specific key branch in the program’s execution. This is accomplished by reverse engineering the compiled program code using a debugger such as SoftICE, OllyDbg, GDB, or MacsBug until the software cracker reaches the subroutine that contains the primary method of protecting the software (or by disassembling an executable file with a program such as IDA). The binary is then modified using the debugger or a hex editor in a manner that replaces a prior branching opcode with its complement or a NOP opcode so the key branch will either always execute a specific subroutine or skip over it. – Wikipedia
Stepping though some of the code, we come across this location which looks like a possible match to the code we’re looking for.
The value of register eax is 0, right after the function call. Let’s modify the value to 1 and continue running the application. The application displays a different error message this time; instead of an invalid license, the application is telling us that it is unable to locate the file.
Now that we have pinpointed the location where the application checks for a valid license, all we need to do is to play around with the values and jmp instructions to find one that works. In this case, inverting the jump instruction from je to jne tells the application that it has a valid license file. Running the application with the modified code displays our new expiration date of March 15, 2012.

Discuss this article here: http://www.rohitab.com/discuss/topic/37059-using-api-monitor-to-crack-copy-protected-software/
What is Password Cracking?
Password cracking is the process of attempting to gain Unauthorized access to restricted systems using common passwords or algorithms that guess passwords. In other words, it’s an art of obtaining the correct password that gives access to a system protected by an authentication method.
Password cracking employs a number of techniques to achieve its goals. The cracking process can involve either comparing stored passwords against word list or use algorithms to generate passwords that match
In this Tutorial, we will introduce you to the common password cracking techniques and the countermeasures you can implement to protect systems against such attacks.
Topics covered in this tutorial
What is password strength?
Password strength is the measure of a password’s efficiency to resist password cracking attacks. The strength of a password is determined by;
- Length: the number of characters the password contains.
- Complexity: does it use a combination of letters, numbers, and symbol?
- Unpredictability: is it something that can be guessed easily by an attacker?
How To Crack Trial Software With Ollydbg Tutorial Beginners Photo Editing Software
Let’s now look at a practical example. We will use three passwords namely
1. password
2. password1
3. #password1$
For this example, we will use the password strength indicator of Cpanel when creating passwords. The images below show the password strengths of each of the above-listed passwords.
Note: the password used is password the strength is 1, and it’s very weak.
Note: the password used is password1 the strength is 28, and it’s still weak.
Note: The password used is #password1$ the strength is 60 and it’s strong.
The higher the strength number, better the password.
Let’s suppose that we have to store our above passwords using md5 encryption. We will use an online md5 hash generator to convert our passwords into md5 hashes.
The table below shows the password hashes| Password | MD5 Hash | Cpanel Strength Indicator |
|---|---|---|
| password | 5f4dcc3b5aa765d61d8327deb882cf99 | 1 |
| password1 | 7c6a180b36896a0a8c02787eeafb0e4c | 28 |
| #password1$ | 29e08fb7103c327d68327f23d8d9256c | 60 |
We will now use http://www.md5this.com/ to crack the above hashes. The images below show the password cracking results for the above passwords.
As you can see from the above results, we managed to crack the first and second passwords that had lower strength numbers. We didn’t manage to crack the third password which was longer, complex and unpredictable. It had a higher strength number.
Password cracking techniques
There are a number of techniques that can be used to crack passwords. We will describe the most commonly used ones below;
- Dictionary attack– This method involves the use of a wordlist to compare against user passwords.
- Brute force attack– This method is similar to the dictionary attack. Brute force attacks use algorithms that combine alpha-numeric characters and symbols to come up with passwords for the attack. For example, a password of the value “password” can also be tried as p@$$word using the brute force attack.
- Rainbow table attack– This method uses pre-computed hashes. Let’s assume that we have a database which stores passwords as md5 hashes. We can create another database that has md5 hashes of commonly used passwords. We can then compare the password hash we have against the stored hashes in the database. If a match is found, then we have the password.
- Guess– As the name suggests, this method involves guessing. Passwords such as qwerty, password, admin, etc. are commonly used or set as default passwords. If they have not been changed or if the user is careless when selecting passwords, then they can be easily compromised.
- Spidering– Most organizations use passwords that contain company information. This information can be found on company websites, social media such as facebook, twitter, etc. Spidering gathers information from these sources to come up with word lists. The word list is then used to perform dictionary and brute force attacks.
Spidering sample dictionary attack wordlist
Password cracking tool
These are software programs that are used to crack user passwords. We already looked at a similar tool in the above example on password strengths. The website www.md5this.com uses a rainbow table to crack passwords. We will now look at some of the commonly used tools
John the Ripper
John the Ripper uses the command prompt to crack passwords. This makes it suitable for advanced users who are comfortable working with commands. It uses to wordlist to crack passwords. The program is free, but the word list has to be bought. It has free alternative word lists that you can use. Visit the product website https://www.openwall.com/john/ for more information and how to use it.
Cain & Abel
Cain & Abel runs on windows. It is used to recover passwords for user accounts, recovery of Microsoft Access passwords; networking sniffing, etc. Unlike John the Ripper, Cain & Abel uses a graphic user interface. It is very common among newbies and script kiddies because of its simplicity of use. Visit the product website https://www.softpedia.com/get/Security/Decrypting-Decoding/Cain-and-Abel.shtml for more information and how to use it.
How To Crack Trial Software With Ollydbg Tutorial Beginners For Beginners
Ophcrack
Ophcrack is a cross-platform Windows password cracker that uses rainbow tables to crack passwords. It runs on Windows, Linux and Mac OS. It also has a module for brute force attacks among other features. Visit the product website https://ophcrack.sourceforge.io/ for more information and how to use it.
Password Cracking Counter Measures
- An organization can use the following methods to reduce the chances of the passwords been cracked
- Avoid short and easily predicable passwords
- Avoid using passwords with predictable patterns such as 11552266.
- Passwords stored in the database must always be encrypted. For md5 encryptions, its better to salt the password hashes before storing them. Salting involves adding some word to the provided password before creating the hash.
- Most registration systems have password strength indicators, organizations must adopt policies that favor high password strength numbers.
Hacking Activity: Hack Now!
In this practical scenario, we are going to crack Windows account with a simple password. Windows uses NTLM hashes to encrypt passwords. We will use the NTLM cracker tool in Cain and Abel to do that.
Cain and Abel cracker can be used to crack passwords using;
- Dictionary attack
- Brute force
- Cryptanalysis
How To Crack Trial Software With Ollydbg Tutorial Beginners Tutorial
We will use the dictionary attack in this example. You will need to download the dictionary attack wordlist here 10k-Most-Common.zip
For this demonstration, we have created an account called Accounts with the password qwerty on Windows 7.

Password cracking steps
- Open Cain and Abel, you will get the following main screen
- Make sure the cracker tab is selected as shown above
- Click on the Add button on the toolbar.
- The following dialog window will appear
- The local user accounts will be displayed as follows. Note the results shown will be of the user accounts on your local machine.
- Right click on the account you want to crack. For this tutorial, we will use Accounts as the user account.
- The following screen will appear
- Right click on the dictionary section and select Add to list menu as shown above
- Browse to the 10k most common.txt file that you just downloaded
- Click on start button
- If the user used a simple password like qwerty, then you should be able to get the following results.
- Note: the time taken to crack the password depends on the password strength, complexity and processing power of your machine.
- If the password is not cracked using a dictionary attack, you can try brute force or cryptanalysis attacks.
Summary
- Password cracking is the art of recovering stored or transmitted passwords.
- Password strength is determined by the length, complexity, and unpredictability of a password value.
- Common password techniques include dictionary attacks, brute force, rainbow tables, spidering and cracking.
- Password cracking tools simplify the process of cracking passwords.
